Im going to go through some DNS stuff tonight. I understand the concept but like anything in IT its a never ending hellscape of ideas as to how it works and eventually you get a feel for it and learn that there are almost never completely hard and fast rules. Funny how the real world works like that too. Anyway, I’m reading to seek some answers that having meaning rather than this goes here. I want to why. Memorization for the sake of memorization has always been and will always be boring to me.
Without futher ado, here are string of articles that are linked by MesureUp. As of this point I haven’t read them but I’m assuming this will work like the last post where the MSFT links where not exactly helpful.
Use DNS Policy for Split-Brain DNS in Active Directory
Use DNS Policy for Applying Filters on DNS Queries
DNS Policies in Windows Server 2016 Tech Preview 2
Use DNS Policy for Application Load Balancing
There are 2 more but they are on the general networking blog which means that they may or may not load correctly. Generally they don’t. Regardless, that’s a lot to read. I’m going to get back to that as, to be honest, im not super familiar with the basic concepts and usually the TechNet articles assume that you are familiar with the basic concepts. So lets outline those.
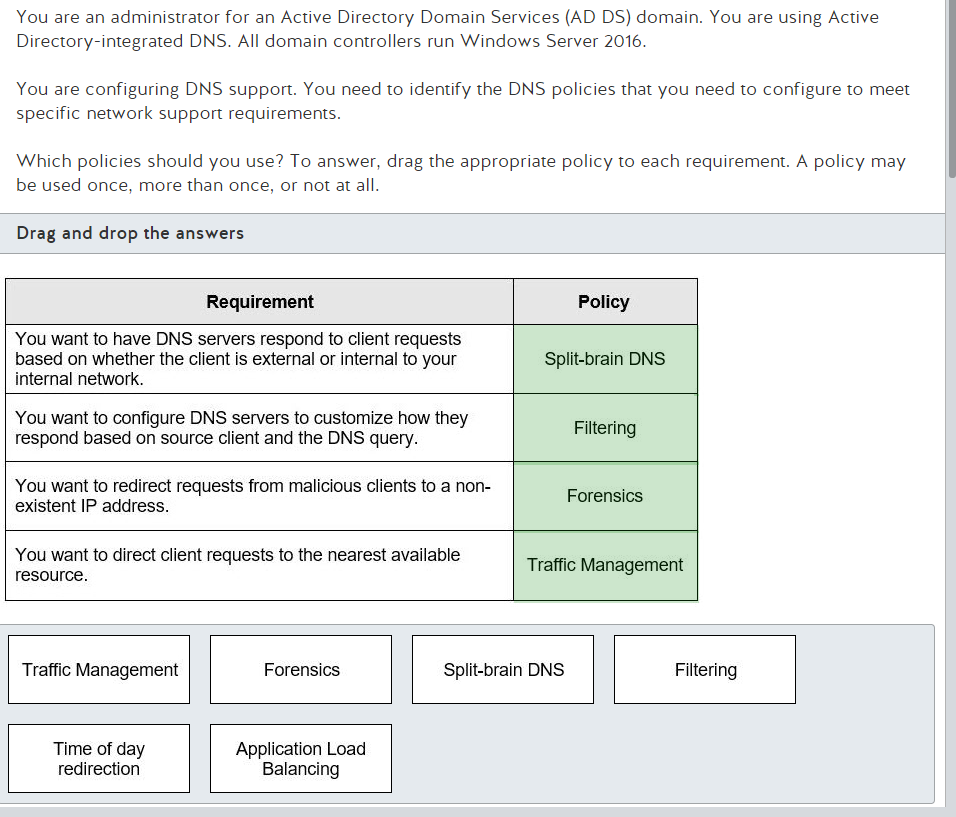
Wow that was short and sweet and to the point and they even used “round robin.” So its a weighted solution that takes into geographical traffic management that accounts for outage to provide the lowest latency response. Very helpful.
Honestly, its a pretty straight forward thing that’s analysis of where traffic was routed to and what caused it. Obviously its not a simple as that but that’s a basic overview. If your familiar with any bit of infosec at all you are aware of what the term forensics means.
The MSFT article linked above is the first google result so I went ahead and read that. It wasn’t helpful toward understanding the basic concept. Here we have the basic concept lined out.
Split-Brain DNS, Split-Horizon DNS, or Split DNS are terms used to describe when two zones for the same domain are created, one to be used by the internal network, the other used by the external network (usually the Internet).
I can handle that concept fairly easily. So, if im understanding this right, you have internal and external servers hosting the same site or application and the DNS server points to the correct version based on being an internal or external client. I like this concept. They drop some words in here that are not exactly the same type of technology but are making a comparison so before you start saying “its like a secondary zone” be aware that it is not the same thing and you should look up what a Secondary Zone is. Slightly confusing if your not up to date on all your definitions. A read only copy of the same zone will not point you to an internal server for resource access. As to all the granular specifics of how the traffic is resolved in split-brain DNS, we will leave that alone for now. You will find that no matter what vector of information technology you pursue there are always more birds to chase down after you’ve figured out the first
one and at some point you have to say “ok for now all I need is this concept”.
This seems pretty straight forward but dear god is this link annoying. Basically its like access control that says certain websites are blocked. The question that the answer to involves this is much more complicated than something as simple as blocking traffic to a website that your company doesn’t want users to have access to. Expectantly given the source client information which is an indicator that this is not a network wide solution. This kind of has me thinking about granular policies and the implications there in. Clearly they are indicating that this has to be fairly specific and in the experience I have with the 3rd party proxy my company uses and how the internal proxies we can set up direct traffic I can assure you this can involve an immense amount of administrative overhead. However, the question then becomes confusing again because what they are describing sounds very similar to split-brain DNS. I’m very close to chalking this up to arbitrary memorization based on a preferred flavor.
DNS Responses Based on Time of Day with an Azure Cloud App Server
When you google this one this is the first thing that comes up. Honestly it seems pretty apparent. At this point they are not asking how to implement it and with that, I’ll take the explanation hence forth which says ‘it changes what server your pointing at based on the time of day.’ Clearly I did not grasp that concept based on the name.
This seems like instance balancing for containers and all the documentation points at AWS stuff, which I found amusing. Obviously AWS tech isnt going to be tested and MSFT has their own balancing tech built into the networking fabric.
So I guess I should read the MSFT stuff now. Ok, I have read through them and honestly the only helpful one, in this case, is the application load balancing one and even that one has a really terrible diagram that makes 0 sense. Like ok, the client is asking for a resource which goes to a DMZ server (I’mm assuming) which is in front of them and then the load hosting servers are not behind that server but rather behind the client asking for access to the resource. lol, perfect. The most confusing thing to me for this one is traffic management. I’m not clear on how this helps sort through geographical resolution however its
quite clear that DNS resolution is a giant time sink so I’m going to leave it at that. I feel good about the terms ‘forensic’ and ‘split-brain DNS’ though.
That’s all for tonight. Nick Barnes signing off. Thanks for your time if you read this, hopefully it was helpful, in some manor of speaking.

Leave a comment