Finally getting around to getting back to this. For some reason decided to write some trap songs and put them over youtube beats. Kind of a waste of time, but whatever. I’ve also been regularly smoking for bout 2 months now. again. Ill take 2-3 days off in a row but generally im still smoking at least one cig a day. I promised my self would stop feb 1st and hear it is, the end of the month. Not sure what’s so stressful or has me concerned enough to think that I should smoke. I mean, I like smoking but there’s really no need for it. So, gotta make that choice to kick that again. Especially if im trying to run a 10 min mile. Gah, its always something with me isnt it? Truthfully, I’ve been around a lot of musicians since I was a young teenager and never recorded my self doing any thing. I wasn’t terribly disappointed with the results but I’m not quitting my day job. Here’s to being an adult. Anyway, lets get to these questions!
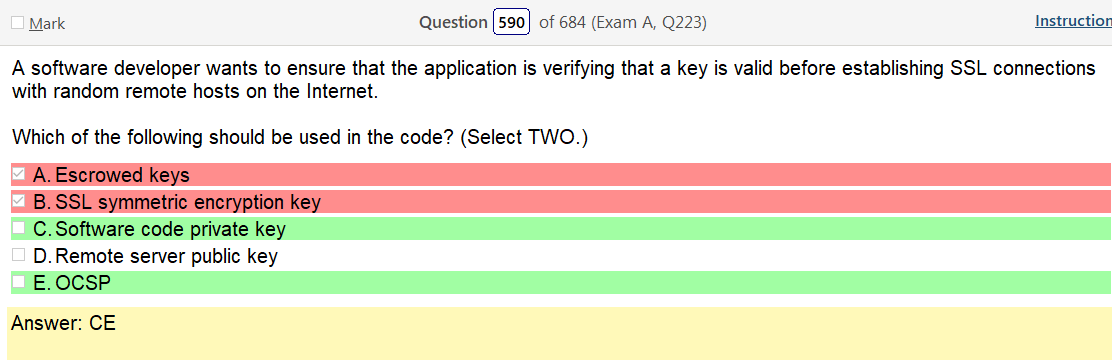
I’m not sure what they mean by key? Encryption key? So lets figure that out: In cryptography, a key is a piece of information that determines the functional output of a cryptographic algorithm. For encryption algorithms, a key specifies the transformation of plaintext into ciphertext, and vice versa for decryption algorithms. The next question is What is the bottom green answer and we have answered that previously but lets cover it again Online Certificate Status Protocol (OCSP) is an Internet protocol used for obtaining the revocation status of an X.509 digital certificate. So the total package answer gets a little sketchy and this is the most direct thing I can find, which is about as clear as mud A cryptographic key that is used with an asymmetric (public key) cryptographic algorithm and is associated with a private key. The public key is associated with an owner and may be made public. In the case of digital signatures, the public key is used to verify a digital signature that was signed using the corresponding private key. There are some questions here about what kind of encryption its using but heres some helpful info on private keys: Asymmetric cryptography, also known as public key encryption, uses two different but mathematically linked keys. The public key is made available to everyone that needs it in an easily accessible repository while the private key is confidential and only shared with its owner. In this method, whatever is encrypted with the public key requires the related private key for decryption and vice versa. Public key encryption is typically used for securing communication channels, such as email. Like theres no indication that its not symmetric encryption
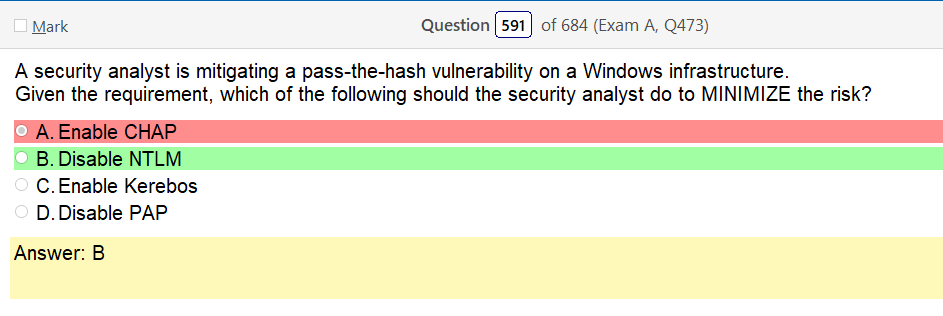
NTLM does have a known pass the hash vulnerability The NTLM protocol uses one or both of two hashed password values, both of which are also stored on the server (or domain controller), and which through a lack of salting are password equivalent, meaning that if you grab the hash value from the server, you can authenticate without knowing the actual password.
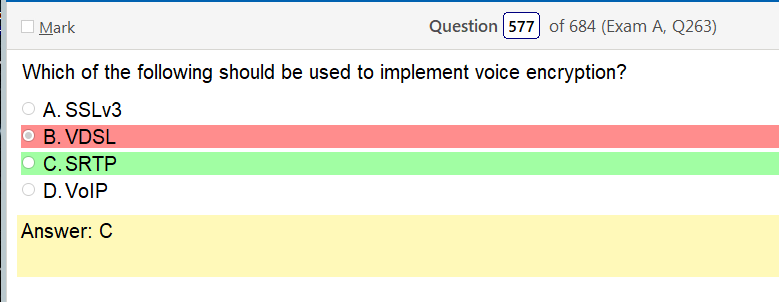
There where two options here that I didn’t know what they where and clearly I picked the wrong one, so lets define those
- VDSL – lol Very high speed digital subscriber line (VDSL)[1] and very high speed digital subscriber line 2 (VDSL2)[2] are digital subscriber line (DSL) technologies providing data transmission faster than asymmetric digital subscriber line (ADSL).
- SRTP – SRTP uses encryption and authentication to minimize the risk of denial of service( DoS ) attacks. SRTP can achieve high throughput in diverse communications environments that include both hard-wired and wireless devices
Obviously I picked the wrong thing and the test question showed up as unhappy.
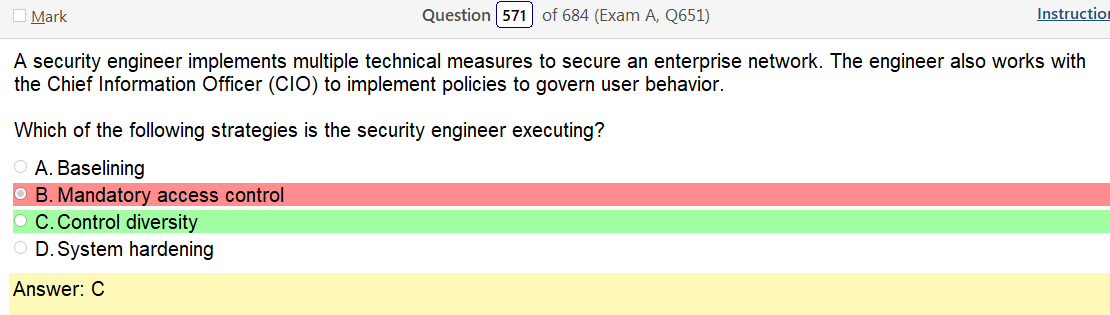
The ‘govern’ word really throws me off here but when looking at the definition off the answer the first sentence does seem to point to that Control diversity is the use of different security control types, such as technical controls, administrative controls, and physical controls. For example, technical security controls such as firewalls, intrusion detection systems (IDSs), and proxy servers help protect a network
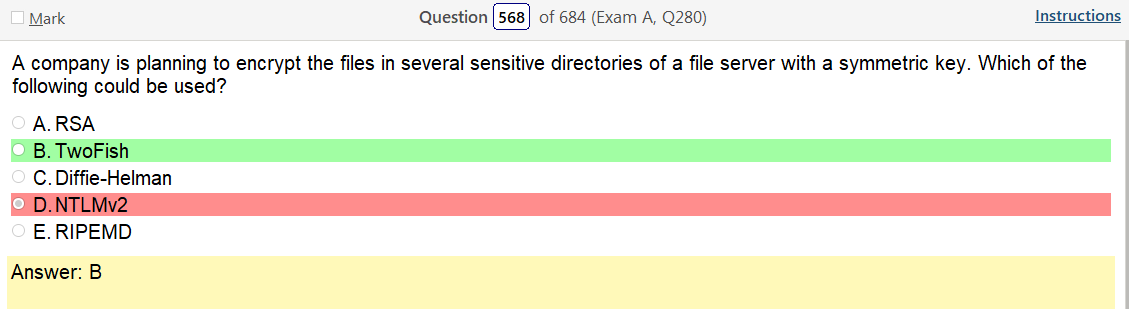
This is one of those confusing things because NTLMv2 does use symmetric key encryption but from what im understanding twofish would be the one out of these that interacts with data at rest.
Well, that’s all for tonight. Hopefully we will meet some time again soon, blog. Absolutely no promises though but im pretty much telling you right now that will never happen. I can do whatever I want but currently I’m choosing to put shitty trap music voice memos in a drop box rather than be productive haha. Nah, thankfully this was less taxing than the others have been lately because some of the questions in the last few posts have been buggers and I would not be surprised if I came back around and blogged the same questions again.

Leave a comment